See Your Entire Identity Attack Surface
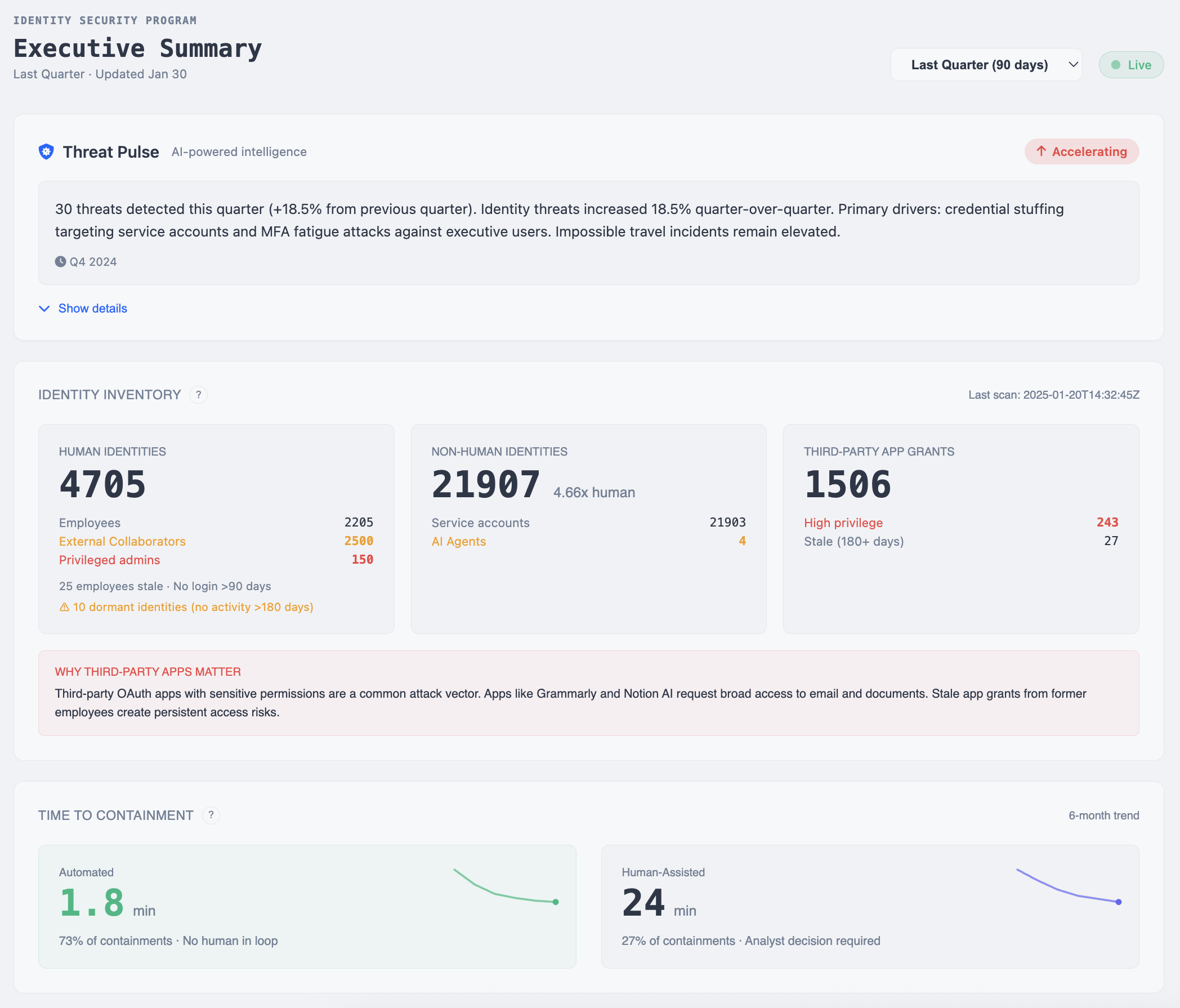
Most organizations don't know how many identities exist in their environment. Auth Sentry Monitor gives you complete visibility into humans, non-humans, OAuth tokens, and everything in between.
One Platform. Every Identity. Complete Visibility.
A medium-sized organization connected Monitor expecting to find around 300 identities. The gap between what you think exists and what actually exists is where risk hides.
Human Identities
Employees, contractors, partners with varying access levels
Non-Human Identities
Service accounts, machine identities, workload identities
OAuth Applications & Tokens
Third-party integrations with persistent access to your data
In most organizations, non-human identities outnumber humans 10:1.
What Auth Sentry Monitor Includes
Your IdP's native reporting only shows what's inside that ecosystem. Monitor connects across providers to build a unified view.
Unified Identity Inventory
Cross-provider visibility in one view. See every identity across all connected systems, not siloed reports from each provider.
Human & Non-Human Classification
Automatic categorization of all identity types. Know exactly what's a person, what's a service account, and what's a machine identity.
OAuth App Discovery
Find every third-party integration with persistent access. Apps like Grammarly and Notion AI request broad access that creates risk.
Stale Identity Detection
Surface dormant and orphaned accounts automatically. Identify accounts with no login in 90+ days or no activity in 180+ days.
Permission Visibility
See access scopes across all connected systems. Understand who has access to what, and spot over-privileged identities.
Identity Relationship Mapping
Which humans authorized which apps. Which service accounts access which resources. Connections that aren't obvious in isolation.
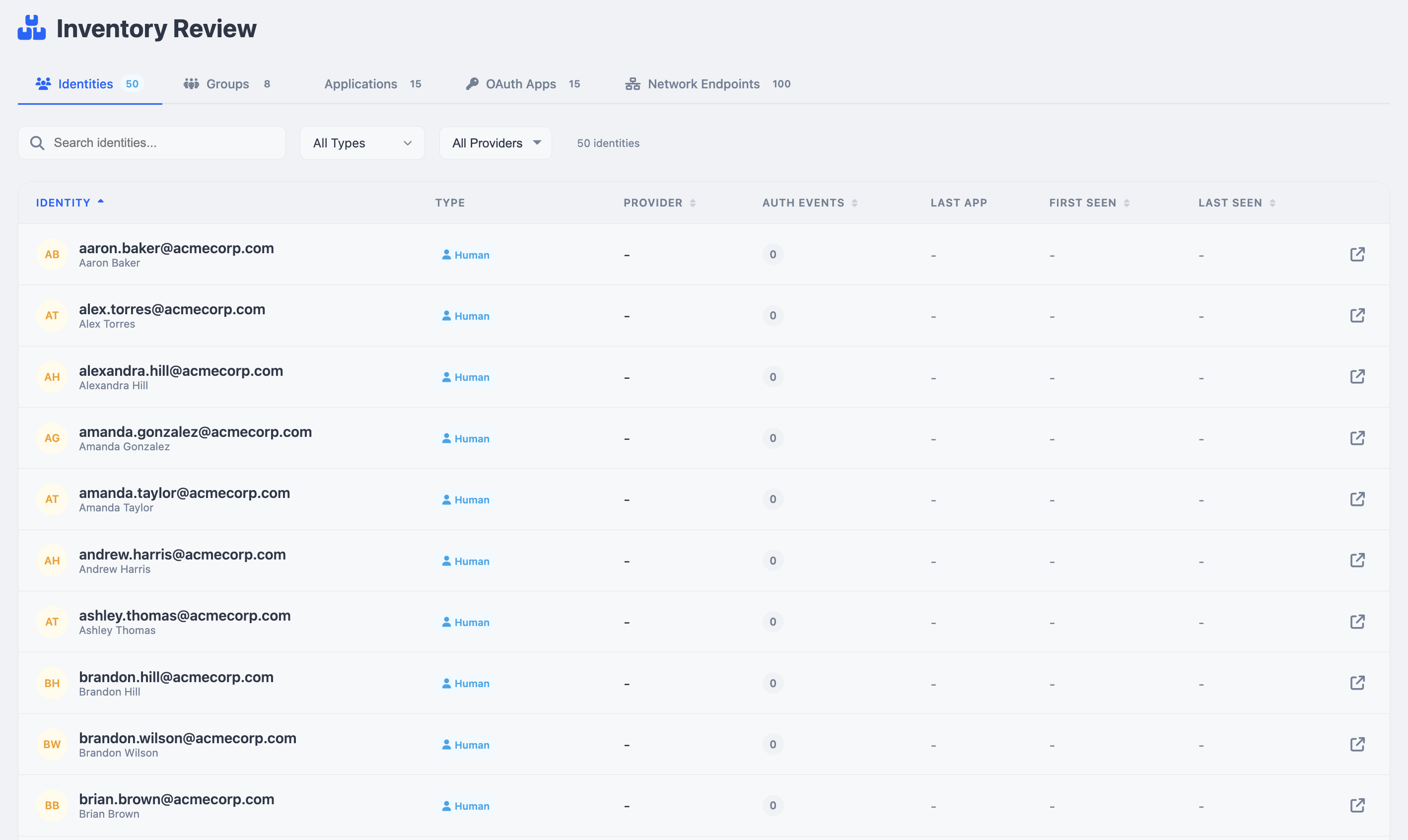
Unified Identity Inventory
See every identity across all connected providers in one searchable view.
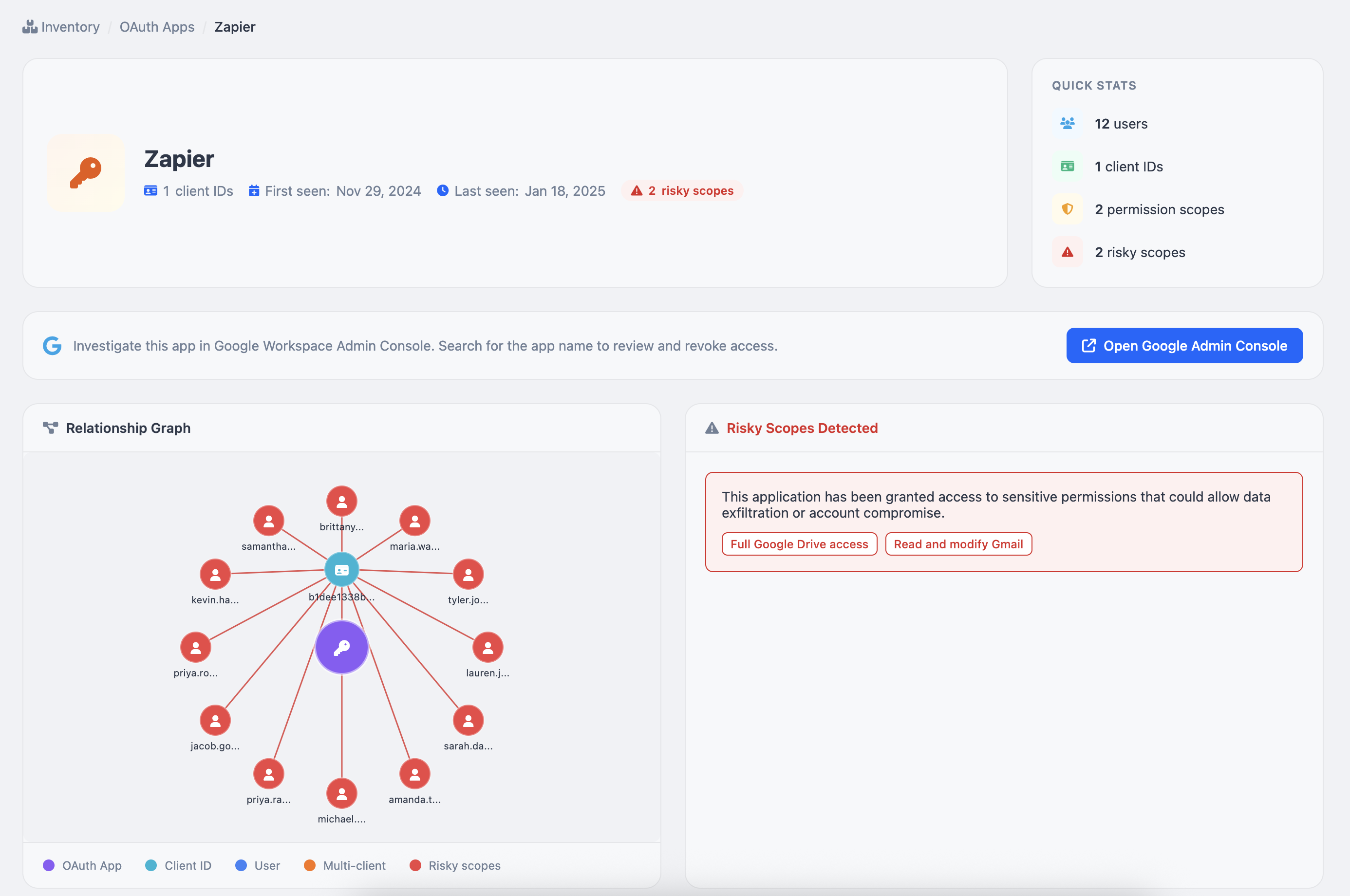
OAuth App Relationship Mapping
Visualize which users granted access to third-party apps and identify risky permission scopes.
Ready to see what's in your environment?
Connect your identity providers and get your complete identity inventory in minutes. No credit card required.
Get Started FreeConnect Your Identity Providers
Launching with support for the most common identity providers.
Read-only access. No agents to deploy. No infrastructure to manage.
Your Data, Secured
Read-Only Access
Monitor only reads identity metadata. We never modify your IdP configuration or user accounts.
Encrypted & Isolated
Data encrypted in transit and at rest. Strict tenant boundaries ensure your data is never mixed with others.
US-Based Infrastructure
Hosted in AWS US-East-2. Delete your account and your data is automatically removed.
For details, see our security policy and privacy policy.
Why We're Making This Free
Visibility shouldn't be a premium feature. Every organization deserves to know what identities exist in their environment. That's table stakes for security, not a value-add.
The team behind Auth Sentry comes from Duo, Censys, and the MDR world. We've lived the identity visibility problem firsthand—and built the tool we couldn't find.
See Your Identity Attack Surface Today
Auth Sentry Monitor is free. No credit card required. Just visibility into what you're actually protecting.
Get Started FreeQuestions? Check our FAQ or reach out at [email protected]