Scattered Spider. LAPSUS$. ShinyHunters. Three of the most effective identity attackers of the past three years have merged tactics under a single campaign—and they're bypassing MFA in real time.
- SLSH vishing attacks bypass MFA by capturing credentials in real time during phone calls
- Attackers enroll their own devices for MFA, then gain SSO access to all connected applications
- Traditional security tools miss these attacks because the login appears fully legitimate
- ITDR detects the attack by correlating device enrollment, IP anomalies, session breadth, and OAuth activity
When SLSH compromised a corporate Okta environment in January 2026, the logs did not show a failed login. They showed a successful one. Valid credentials, MFA passed, new session opened. From a traditional security tool's perspective, an authorized employee had just signed in. That is not a detection failure. It is the design of the attack. And it is exactly why identity threat detection and response (ITDR) has become essential for organizations that rely on SSO.
Google's Mandiant confirmed the campaign publicly on January 28, 2026. CTO Charles Carmakal described it directly: "Mandiant is tracking a new, ongoing campaign using evolved voice phishing techniques to successfully compromise SSO credentials from victim organizations, and enroll threat actor controlled devices into victim multifactor authentication solutions. This is an active and ongoing campaign."[1]
How the Attack Works, Step by Step
Silent Push, which first detected the attack infrastructure on January 26, 2026, described what they found: "This isn't a standard automated spray-and-pray attack; it is a human-led, high-interaction voice phishing operation designed to bypass even hardened Multi-Factor Authentication setups."[2] The mechanics break down like this:
- An attacker calls an employee posing as IT staff. The pretext is mundane: the company is updating MFA settings and the employee needs to complete a verification step.
- The employee is directed to a victim-branded credential harvesting site, a pixel-perfect replica of the company's Okta or Entra login page. Domains follow patterns like companyname-sso.com or companyname-internal.com and are registered to look legitimate, with HTTPS and the real company logo.
- A Live Phishing Panel, operated by a human attacker in real time, sits between the victim and the real identity provider. Credentials and MFA codes are captured and replayed instantly to complete the legitimate login, while the employee is still on the call.
- Okta's own threat researcher Moussa Diallo explained the panel's capability: "Using these kits, an attacker on the phone with a targeted user can control the authentication flow while that user interacts with credential phishing pages. They can control the pages the target sees in their browser in perfect sync with the instructions they provide during the call. The threat actor can use this synchronization to defeat any form of MFA that is not phishing-resistant."[5]
- The attacker enrolls their own device for MFA. Mandiant observed that attackers then deleted the confirmation email Okta sends automatically, so the employee never sees the notification.
- Because this is an SSO session, the attacker now holds a skeleton key. Every connected application, including Slack, Teams, GitHub, cloud consoles, Salesforce, SharePoint, and internal dashboards, is accessible without additional authentication.
- From inside Slack or Teams, the attacker impersonates the compromised employee to social-engineer higher-privilege administrators, requesting credential resets or access grants under plausible business pretexts.
- Mass data exfiltration follows. Then the extortion demand.
Employees who fall for this are not making careless mistakes. They are being targeted by a skilled human attacker with a professional script, a convincing fake portal, and real-time control of what appears in their browser. Training reduces risk at the margins. Detection after authentication is the only reliable defense.
What Defenders Need to Look For
Mandiant published a detailed hardening and detection guide alongside its January advisory.[3] The forensic signatures SLSH leaves behind are identifiable, but only if you are monitoring the right signals across identity systems rather than relying solely on endpoint or network telemetry. This is where ITDR platforms differentiate from traditional SIEM or EDR tools.
Signal 1: New Device Enrollment Followed by an Anomalous Login
Mandiant flagged this pattern specifically. In a legitimate MFA update, device enrollment and the first subsequent login share consistent session context and source IP. In an SLSH attack, enrollment is followed almost immediately by a login from a previously unseen IP, often in a different geography. Mandiant documented that attackers deleted the Okta confirmation email to suppress this signal from the employee's inbox.[4] Forensic analysis of these attacks typically shows the window between enrollment and first suspicious access measured in seconds to minutes, not hours.
Signal 2: SSO Session Touching an Unusual Breadth of Applications
A real employee logs into Okta and accesses the handful of apps they use every day. A compromised SSO session starts accessing applications the user has never touched, or accesses them in an order that does not match any prior pattern. Mandiant documented attackers using the SSO dashboard as a springboard into Salesforce, Microsoft 365, SharePoint, DocuSign, Slack, Atlassian, Dropbox, and Google Drive in a single session.[4] Cross-application session analysis catches this. Most SIEMs do not have the identity log depth to surface it.
Signal 3: Internal Messaging Activity Outside Normal Patterns
After initial access, SLSH pivots to Slack or Teams to escalate privilege through social engineering. Unusual direct message volume, messages sent to administrators from an account with no prior relationship with those administrators, and after-hours activity spikes are all worth correlating against the identity event that preceded them.
Signal 4: OAuth Application Authorizations During an Anomalous Session
In earlier SLSH campaigns targeting Salesforce, attackers abused OAuth consent flows during vishing calls to silently authorize attacker-controlled applications. A new OAuth app authorization on an account with no history of authorizing apps, especially one requesting broad data scopes, is a high-fidelity signal that most organizations are not actively monitoring.
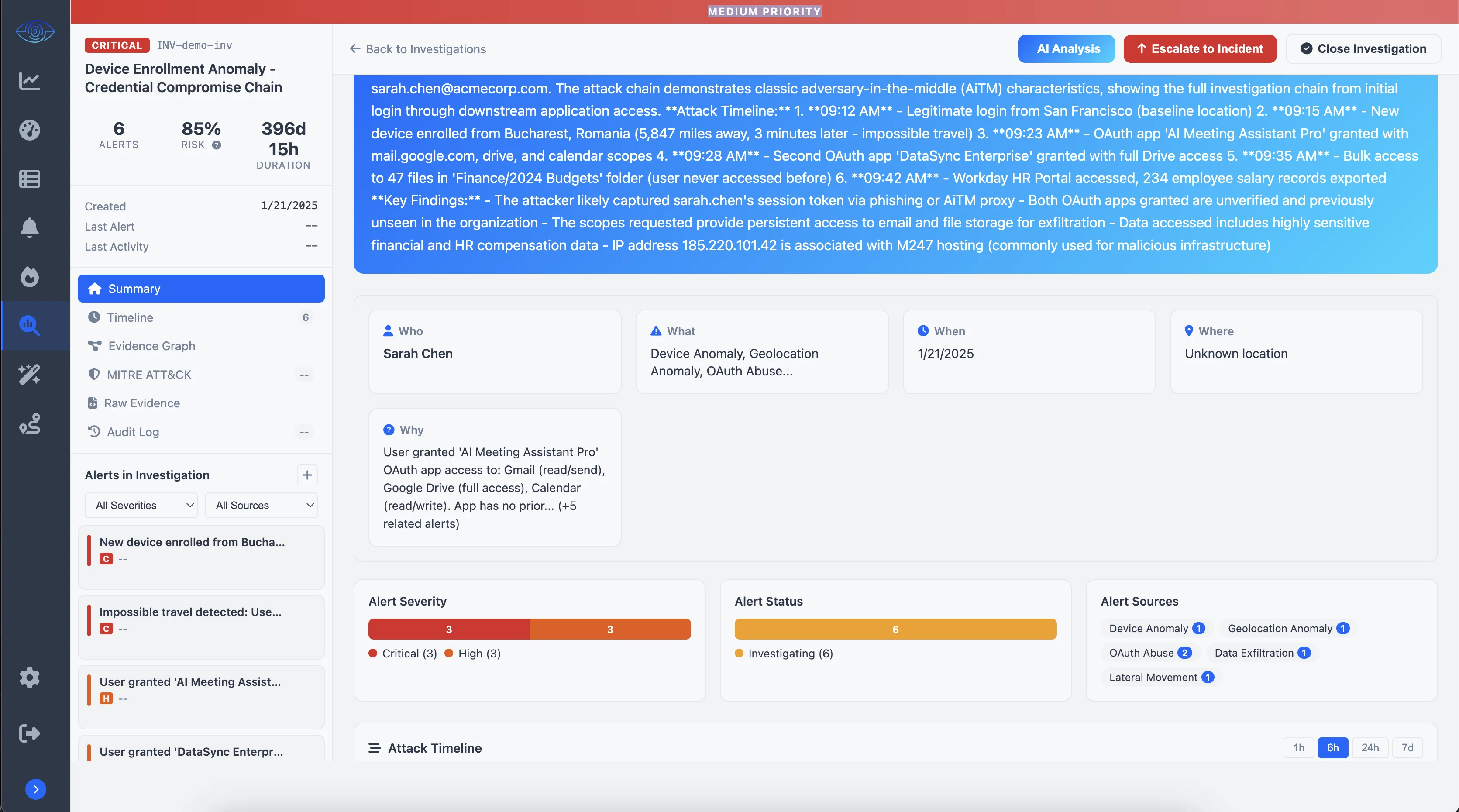
A typical SLSH investigation in Auth Sentry.
Why Alerting Alone Does Not Work
Each of these signals in isolation can look like noise. A traveling employee logs in from a new IP. An admin authorizes an unfamiliar OAuth app. A new device gets enrolled when someone switches phones.
Mandiant put it plainly in their defensive guidance: "If an adversary gains access through vishing and MFA manipulation, the first reliable signals will appear in the SSO control plane, not inside a workstation. Without clear visibility into these environments, detection becomes nearly impossible. If an organization cannot track which identity authenticated, what permissions were authorized, and what data was exported, they often remain unaware of a campaign until an extortion note appears."[3]
The investigation has to connect the enrollment event to the IP anomaly, to the SSO session breadth, to the OAuth authorization as a single correlated chain before it registers as a threat. That work takes a SOC analyst hours to do manually, well after the attacker has already moved laterally and started exfiltrating data. This is the core problem ITDR solves: correlating identity signals across systems and presenting complete investigations, not raw alerts.
Have questions about SLSH, ITDR, or how to protect your organization? See our frequently asked questions.
Sources
- CyberScoop. "A New Wave of Vishing Attacks Is Breaking Into SSO Accounts in Real Time." cyberscoop.com
- Silent Push. "Special Alert: SLSH Malicious Supergroup Targeting 100+ Organizations via Live Phishing Panels." January 26, 2026. silentpush.com
- Mandiant / Google Cloud. "Proactive Defense Against ShinyHunters-Branded Data Theft Targeting SaaS." cloud.google.com
- BleepingComputer. "Mandiant Details How ShinyHunters Abuse SSO to Steal Cloud Data." bleepingcomputer.com
- Okta Threat Intelligence. "Phishing Kits Adapt to the Script of Callers." January 2026. okta.com
How We Built Auth Sentry to Detect This
We built Auth Sentry because we have been on the other side of these investigations. Our team comes from Duo, Censys, Expel, and Rapid7, and we have seen how hard it is to correlate identity signals across systems when you are relying on SIEM queries and manual investigation.
Auth Sentry Monitor connects to Okta, Microsoft Entra ID, Google Workspace, CrowdStrike, and SentinelOne via API. It correlates the signals described in this article automatically: device enrollment timing, session context, application access breadth, and OAuth authorizations. When a pattern like SLSH emerges, you get a complete investigation with evidence timeline, not a queue of disconnected alerts.
When Auth Sentry detects a correlated threat, analysts can revoke SSO sessions, reset device enrollments, and trigger response playbooks directly from the investigation view. Detection and response in one workflow.
Try Auth Sentry Monitor Free
Monitor is free for teams getting started with identity threat detection. Connect your first identity source in minutes and see what is happening across your SSO environment. No credit card required, no sales call needed to get started.
When you need advanced detection rules, automated response actions, or coverage for larger environments, paid tiers are available. But Monitor gives you real visibility from day one.
Get Started Free